March 30, 2026
Your Phone Is Ringing. Nobody's Answering. AI Fixes That.
Your Phone Is Ringing. Nobody's Answering. AI Fixes That.
Read More →
OpenClaw has a security problem. Not a fatal one, but a real one.
It's the fastest-growing open-source project in history, with over 316,000 GitHub stars in under five months. It runs with root-equivalent access on tens of thousands of machines. And in a single four-day stretch in March 2026, nine CVEs were publicly disclosed, including a 9.9 critical that let any authenticated user self-declare admin privileges.
The open-source community patches fast. But enterprise security teams don't sleep well when the tool running shell commands on their network has a CVE tracker with 128 advisories still awaiting assignment.
Two major players have stepped up with answers: NVIDIA with NemoClaw, and Red Hat with their BYOA (Bring Your Own Agent) architecture on OpenShift AI. Both solve the same fundamental problem. They just approach it from completely different directions.

Jensen Huang unveiled NemoClaw at GTC 2026, calling it NVIDIA's enterprise security wrapper for OpenClaw. The pitch is straightforward: take the agent you already have and lock it in a box with strict rules about what it can touch.
The architecture has three layers:
Layer 1: Sandbox (OpenShell). Every agent runs inside an isolated container. It physically cannot access files outside /sandbox and /tmp. It cannot make network requests to unapproved endpoints. It cannot escalate privileges. These boundaries are enforced at sandbox creation, not at the prompt level. The access model is deny-by-default: the agent starts with zero permissions and you explicitly approve what it can reach.
Layer 2: Guardrails. A policy engine that controls three things: what enterprise systems the agent can connect to (Office 365, GitHub, Jira), what actions require human approval, and what data classification rules apply. You define policies once in YAML, and every agent in the stack operates within those boundaries.
Layer 3: Privacy Router. Every model API call gets intercepted before it leaves the sandbox. Sensitive data, including PII, financials, and proprietary code, stays local running on Nemotron or other open-source models like Llama. Non-sensitive queries can optionally route to cloud models like OpenAI or Claude. Everything gets audit logged.
The key insight: NemoClaw isn't just for OpenClaw. It's a platform for running any AI agent safely. OpenClaw, Claude, Cursor can all run side-by-side in their own sandboxes. You install it with a few CLI commands and you're running.
Launch partners include Cisco, CrowdStrike, Salesforce, Adobe, SAP, and Box. That's not a toy ecosystem.
Red Hat's approach, published in their "Operationalizing BYOA on Red Hat AI" series, takes a fundamentally different philosophy. Instead of wrapping the agent in a secure box, they build the entire platform that the box runs on.
The key components:
Kata Containers. Kernel-level isolation per agent session, providing hardware-enforced boundaries (not just container namespaces). Similar goal to NemoClaw's sandbox, but implemented at a deeper infrastructure layer.
SPIFFE/SPIRE for Identity. Cryptographic workload identity for every agent and service. No hardcoded API keys. No shared secrets. Each agent gets a verifiable identity certificate that determines what it can access.
MCP Gateway. This is the star of the show. An Envoy-based proxy that sits in front of all MCP (Model Context Protocol) servers as a single endpoint. Agents set one MCP_URL environment variable and get an aggregated tool catalog. But which tools they can actually call is determined by their token claims, not by anything in the prompt.
This is the critical security insight: prompt injection attacks that trick an agent into calling unauthorized tools get stopped at the infrastructure layer. The gateway doesn't read prompts. It validates token claims. A jailbroken agent can "want" to call a dangerous tool all day long. The gateway simply won't route the request.
Full Safety Lifecycle. Red Hat doesn't stop at runtime. They build a complete pipeline:
| NemoClaw | Red Hat BYOA | |
|---|---|---|
| Target audience | Teams, individual machines, DGX Spark | Enterprise, multi-tenant Kubernetes |
| Setup complexity | CLI install, minutes | OpenShift deployment, days |
| Isolation model | Container sandbox (OpenShell) | Kata Containers (kernel-level) |
| Identity | YAML policy, deny-by-default | SPIFFE/SPIRE cryptographic identity |
| Tool governance | Policy engine in sandbox | MCP Gateway (infrastructure-level) |
| Prompt injection defense | Sandbox prevents execution | Gateway ignores prompts entirely |
| Inference routing | Privacy router, local-first on Nemotron | vLLM/OpenResponses, self-hosted |
| Pre-deploy scanning | Not included | Garak adversarial scanning + CI/CD |
| Observability | Audit logs | MLflow + OpenTelemetry |
| Multi-agent support | Yes (OpenClaw, Claude, Cursor) | Yes (any agent via Kagenti operator) |
| Enterprise partners | Cisco, CrowdStrike, Salesforce, SAP, Adobe, Box | Red Hat/IBM ecosystem |
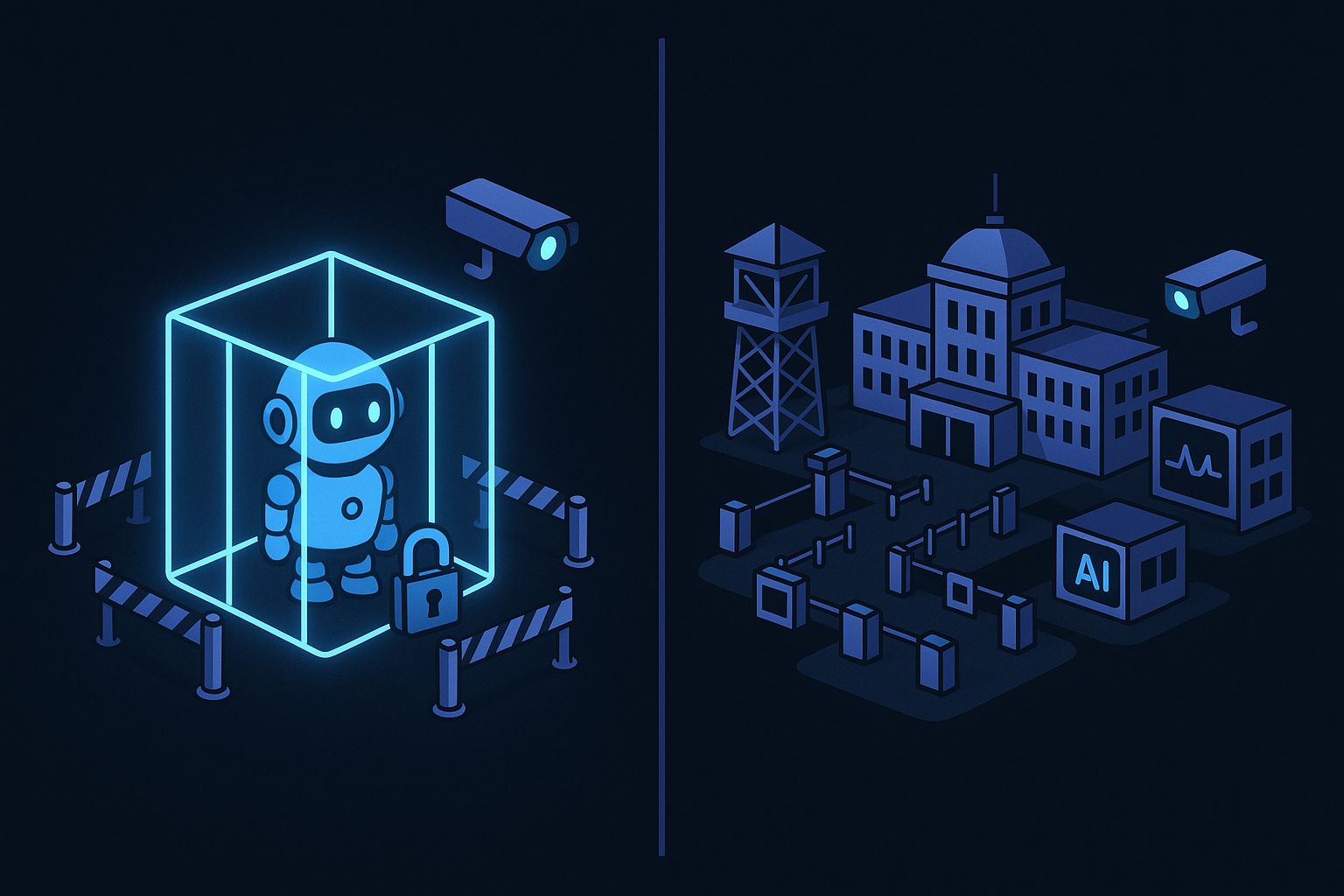
NemoClaw is "put your agent in a cage." Red Hat is "build the entire prison system with intake screening, monitoring, and parole policies."
Neither is wrong. They're solving for different scales and different threat models.
NemoClaw says: "Your agent is dangerous. We'll contain it." The sandbox approach is intuitive, fast to deploy, and works well for teams that need security today without redesigning their infrastructure. If you're running OpenClaw on a workstation or a DGX Spark and you need it enterprise-safe by Friday, NemoClaw is the answer.
Red Hat says: "Your entire platform needs to be secure, and agents are just another workload." The Kubernetes-native approach is more complex to set up, but it scales to hundreds of agents across multiple teams with centralized policy, identity, and observability. If you're an enterprise running OpenShift and you need to govern AI agents the same way you govern microservices, Red Hat's architecture is the answer.
If you're a 10-person company, neither of these is built for you (yet). But the principles matter.
The fact that NVIDIA and Red Hat, two companies with a combined market cap north of $3.5 trillion, are both racing to solve AI agent security tells you where the market is heading. AI agents are moving from "cool demo" to "production infrastructure." And production infrastructure requires production security.
For small businesses, the practical takeaway is simpler: AI agents are powerful enough that the biggest companies in tech are building security infrastructure specifically for them. The tools are real. The capabilities are real. And the companies deploying them with proper security are going to have a massive advantage over those that don't.
The question isn't whether to use AI agents. It's whether you're deploying them with the right guardrails.
We'll analyze your workflows and show you exactly where automation can save you time and money.
Get Your Free Audit